Secure Application Delivery for Any Digital Workspace.
Simply & securely deliver all your business-critical apps to any device, from the browser, so your people can stay productive from anywhere.
Get the Latest Analyst Research
Trusted by Organizations Worldwide
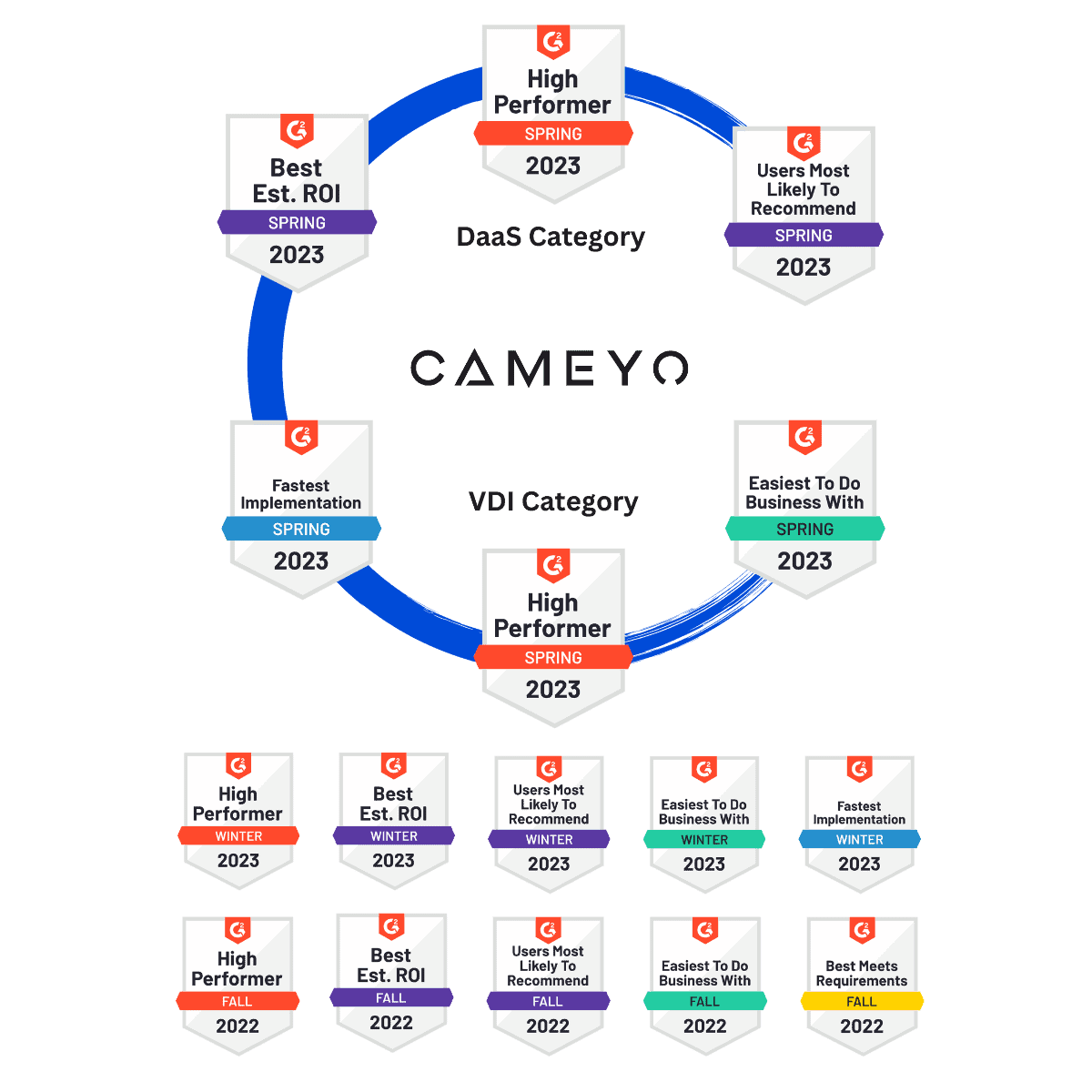
A recent survey of hundreds of Cameyo customers globally revealed industry-leading customer satisfaction.
%
Of Respondents Would Recommend Cameyo
Average Customer Rating
Net Promoter Score
“Cameyo’s platform plays a critical role in enabling our Digital Workplace strategy by removing the legacy application roadblocks that were preventing widespread Chrome adoption here at Sanmina.”
Mario Zúñiga, IT Director, Digital Worplace

“Cameyo brings dramatic cost savings compared to virtual desktop products based on the amount of time it saved us in deployment, ease of ongoing management, and the fact that everything is included – we don’t need to tack on additional third-party tools.”
Christian Ahlin, Group Head of IT

“Cameyo’s Virtual App Delivery (VAD) technology gives us a streamlined cloud desktop allowing users to access all of the apps and data they need to be productive from anywhere – all without the Windows desktop.”
Brian Stopinski, Corporate IT Operations Director






The Cameyo Difference
Simple
Get started in minutes and deploy apps to users in hours, not weeks or months. Even easier for the end user.
Secure
Architected with a Zero Trust security model, eliminating the need for VPNs or open firewall or server ports.
Cost-effective
Cloud-native design with usage optimization and elasticity reduces cost up to 70% over legacy VDI and DaaS products.
Flexible
Cloud-native service works in any cloud or on-premises environment and integrates with your SSO, databases, etc.
All your apps on any device for anytime, anywhere productivity.
Securely deliver ALL your apps – Windows, Linux, SaaS, and internal web apps – to any device to ensure your people can be productive from anywhere. All without the cost, complexity, or security concerns of traditional virtual desktops or VPNs.
The ultimate in flexibility.
Run Cameyo as a fully-hosted service or self-host Cameyo in your own cloud, hybrid or on-premises environment for ultimate flexibility.
A seamless app experience to enhance productivity.
Enable your users to access the full desktop version of all their apps either from the browser or as Progressive Web Apps (PWAs). Your users get a seamless app experience with nothing new to learn, just as if the app was installed locally.
Enabling MSPs and large IT departments to manage multiple customers & divisions.
Manage all your customers (or company divisions) from a single pane of glass, deliver seamless software updates to eliminate on-site visits, and provide simplified billing with a single SKU.
Web enable your software with zero development.
Independent Software Vendors (ISVs) use Cameyo to deliver their software as a service – without any redevelopment costs – and offer instant free trials from their websites to dramatically increase conversions.
Press & Analysts on Cameyo
“The language their customers use is consistent: Cameyo is low cost, simple and easy to use, fast to deploy, secure, and isn’t aggravating. It is like a collection of best practices in a solution.”
“Cameyo’s technology allows companies to set up employees to work from home without needing VPNs and the corresponding software on every laptop or desktop… and can be installed in hours for hundreds of employees.”
Awards & Recognition






See for yourself. Try Cameyo for free.
No software to download or install, and no credit card required. It’s so easy to get started, you’ll have your first app published in less than 10 minutes.