The COVID-19 pandemic has brought about a paradigm shift in the way people work, go to school, and socialize. Keying in on businesses, organizations have had many changes and adjustments to make this year that have affected business-continuity across the board. Remote work has become the new normal of how employees carry out everyday tasks. The shift to remote work has exposed many challenges for organizations managing remote workers and accessing digital resources.
Many businesses had difficult decisions to make a quick shift to remote work for employees. One of those decisions was how employees would be allowed to access corporate systems. Some organizations may have quickly issued corporate devices to their employees. Others may have decided to allow employees to use personal devices for accessing corporate data, remote desktops, and other business-critical resources. Either way, there can be challenges. What are the challenges of company-managed devices vs. non-managed devices?
Challenges of company-managed devices vs. non-managed devices
There is arguably no right or wrong answer to the question of using company-managed devices vs. non-managed devices. Different organizations and business needs often lead to different answers to that question. Due to the suddenness of how the COVID-19 pandemic came upon the business world, organizations that may have otherwise used company-managed devices may have decided to allow remote employees to use personal, non-managed devices for expediency. There may not have been enough time or resources available to provision the number of managed devices needed in a short time. Let’s examine the following questions:
- What best practices should organizations follow for company-managed devices
- What are the security risk differences between company-managed and personal devices?
- Are VPNs an acceptable solution for personal devices accessing corporate resources?
- Is there a secure way to allow personal device access?
1. What best practices should organizations follow for company-managed devices?
Many would agree that company-managed devices provide the best security for end-users and corporate data. When it comes to company-managed mobile devices, there are certain best practices that your business can follow to ensure the most secure device for your end-users. These include the following:
- Require data encryption for the device – Encrypting a mobile device protects against a lost or stolen device. If sensitive corporate data exists on a mobile device, you do not want this to fall into the wrong hands.
- Enforce robust security features – If the mobile device is company-owned, the organization can enforce best practice security measures using MDM software to implement security best practices. It may include requiring strong passcodes and other features.
- Manage third-party applications – Third-party applications are arguably one of the most dangerous components of accessing business-critical data using a mobile device. With the rise of cloud environments, third-party app stores, and the easy means to install and grant access to third-party applications, organizations must protect their data from unwanted access. Attackers are increasingly using malicious applications to compromise data. With the rise of the cloud and easy OAuth permissions delegation, an end-user can grant access to sensitive organization data to a potentially malicious or “leaky” application with just a few clicks.
- Require security software – Security software on mobile devices is crucially important. While it is not an “end all be all” solution to all security threats, it provides a security layer as part of the overall security solution. Organizations certainly want to require security software on all company-owned devices for a healthy security posture.
- Audit mobile device usage and data – This is not saying that organizations play “big brother” over employee activities. However, having the ability to audit use provides a useful tool for forensics and other security investigations. It does also help to engender accountability with end-users who are making use of corporate devices.
2. What are the security risk differences between company-managed and personal devices?
As mentioned at the outset, businesses may have had a difficult decision to make with the global pandemic’s rapid onset. There may not have been enough time to provision and disperse company-managed devices for all employees. With that being the case, organizations may have decided to allow the use of personal, unmanaged devices for a subset or even all remote employees. What are the security risk differences between company-managed and personal devices?
One of the apparent initial considerations that businesses know when asking end-users to use personal devices for corporate access is they cannot enforce the same levels of security that are possible with company-managed devices. Companies cannot mandate the same level of control on a personal device paid for by an end-user. What are the risks of allowing end-users to use personal devices to access business-critical services and data?
- End-users use personal devices for personal activities – End-users use personal devices for personal activities and communications. By default, this means the intermingling of personal device usage and business operations. From a security perspective, this can be risky.
- They may not have mobile device security software installed – End-users may not run security software on their device. Some users may not want any security software installed on a personal device, which is their choice. However, if the end-user performs business activities on the device, this is certainly a point to consider.
- Weak passwords and passcodes – For convenience and ease of use, end-users generally set weak passcodes and other passwords on personal devices. It can lead easy compromise by malicious websites, applications, and other means.
- Personal devices may have unscrupulous or outright malicious third-party software installed – Personal devices may have a wide range of potentially unwanted programs (PUPs) installed. End-users may install risky app store apps and grant high levels of access to mobile device storage.
- They often contain connections to personal cloud and other data sharing tools – Most end-users use personal cloud storage and services. It means that corporate data accessed from a personal device can easily be copied to personal storage locally or a personal cloud environment.
3. Are VPNs an acceptable solution for personal devices accessing corporate resources?
Are VPN connections the answer to securing personal devices used for business access? Some organizations with traditional infrastructure may think so. However, when thinking about the mass shift to remote work, VPN connections can be cumbersome, not scalable, and even problematic to secure mobile device access. There are many reasons for this.
A traditional VPN (Virtual Private Network) creates an encrypted tunnel between the end-user device and the corporate network. While it does secure the tunnel between the two, it also creates inherent security risks for your corporate network. VPNs allow the end-user device to become a part of the corporate network. It means the end-user mobile device has network access similar to being patched into the corporate network itself. With VPN, all third-party software and even malicious applications installed on an end user’s device connect directly to your corporate network.
Additionally, VPN connections can make it easy for an end-user to accidentally or intentionally copy sensitive data from a sanctioned corporate network to their device or personal cloud environment. The capability to directly access data and copy between corporate and personal environments elevates the risk of data leaks. In turn, it leads to the risk of compliance violations and the exposure of sensitive data that can negatively impact your business for years to come.
4. Is there a secure way to allow personal device access?
If an organization has allowed the use of personal, unmanaged devices for accessing corporate data, is there a secure way to allow access for end-users? Organizations need to note that most end-users need access to applications instead of carte blanche access to the corporate network or full-blown desktop environments. There is a secure way for organizations to access corporate data and environments from personal devices – application virtualization.
Modern application virtualization virtualizes applications in such a way that end-users access them from a modern web browser. It means the data stays in the corporate environment. End-users do not have access to the underlying data storage to copy files to personal storage. Additionally, data encryption happens between the device and the corporate-held application through an encrypted browser session. It prevents the entire device from becoming part of the corporate network.
Application virtualization also creates much more efficient use of resources. Virtualizing full desktops is often inefficient since users only need access to applications. By virtualizing the applications, organizations can create a much denser environment to provide remote end-users access to business-critical applications.
Cameyo secure virtual app delivery
Cameyo’s Digital Workspace platform utilizes a Virtual App Delivery approach and provides intrinsic security as part of the solution, not a bolt-on module. It delivers an ultra-secure and efficient digital workspace for organizations supporting remote workers for a wide range of applications, including custom on-premises applications, serverless apps, and even publicly available applications. It can modernize traditional applications and deliver these without the need for VPNs.
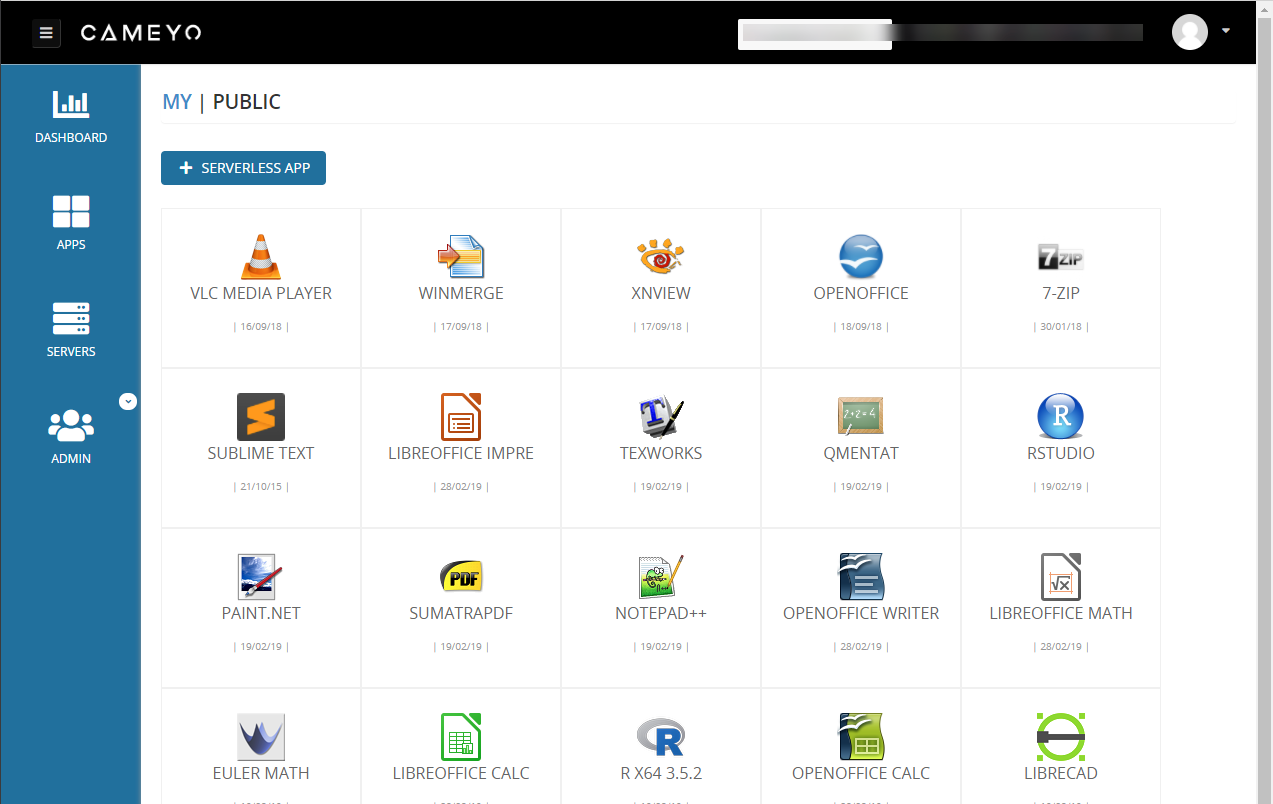
Cameyo allows quickly creating a digital workspace for your remote end-users
For organizations that may have decided to allow using personal devices to access corporate data, Cameyo ensures safe boundaries between business environments and personal devices. How does Cameyo ensure security for remote end-users accessing applications?
- Cameyo NoVPN – Requires no VPN connection to deliver applications. It makes use of a secure HTTPS web browser connection
- Cameyo Port Shield – Unique to Cameyo, Port Shield blocks access to HTTP/S and RDP ports across the board. Only authenticated sessions are allowed to access Cameyo-provided applications.
- Cameyo Layered Revert – A volatile layer that protects the Cameyo server and business-critical data from any malicious activity.
- Cameyo Session Sync – Allows end-users to access specific configuration settings and user files that will follow them between sessions. Session Sync works in harmony with Layered Revert to ensure user data is persistent while making sure the session layer is pristine and secure upon each new connection
Concluding Thoughts
Organizations have had many important decisions to make since the onset of the pandemic. Deciding how to empower remote end-users to access business-critical resources has been one of those decisions. Due to the rapid nature of the shift to remote work, organizations may not have had the time or resources to deploy company-managed devices for all users. Personal devices may have been allowed to access corporate applications and services.
Virtual App Delivery provides a powerful way to access corporate resources from personal devices securely. Cameyo’s Digital Workspace is unique in that it has security designed into the core of the platform. It helps to ensure remote workers can only access the applications needed while protecting the underlying data.
